Israeli espionage after Epstein
Corbett Report
Verdict collapsed: Epstein was a spy!
And against it what media mainly say, he did not produce a compromise for his KGB comrades, alternatively traded for his friends, Israelis.
In addition to many, many ties to Israel, which I mentioned in my article "10 Things I Learned From Epstein Files editorial", more and more data shows how Epstein worked with his friend (and erstwhile Israeli Prime Minister) Ehud Barak to safe contracts and accomplish diplomatic goals for Israel. This data shall include information on how Epstein:
Moreover, the Israeli Government installed and maintained the safety system In an flat in Manhattan that Epstein frequently rented to Barak.
Yes, whatever Epstein was doing, it seems he worked conscientiously behind the scenes as an influence agent, promoting Israel's interests around the world.
But Epstein is dead, as you may have heard. So how will Israel exercise power and influence over abroad diplomats and businessmen now that they can no longer trust on their favourite fixer?
It turns out that the answers to this question can besides be seen in Epstein's file...
CARBYNE Squad
Last November, San Francisco Standard published "Inside the extended courtship between Jeffrey Epstein, Peter Thiel and Israeli officials". The article describes in item how the Handala ("a hacker group associated with Iran") obtained e-mails from Israeli officials, which show that Epstein was again a road grease for the Israeli deep state in their effort to get the broligarchs to himself from Silicon Valley.
First, Epstein sought Thiel's favor:
By 2014, Epstein had a relation with Thiel. According to a copy of Epstein's calendar obtained by The fresh York Times, both had at least 3 meetings scheduled only in September of this year.
In retrospect, they started a business together: within a year after these meetings, Epstein invested $40 million in Valar Ventures, a company that Thiel co-founded, According to The fresh York Times. Thiel was not charged with any wrongdoing associated with his relation with Epstein.
He then introduced Thiel to Barak:
In 2014, Epstein was willing to combine his 2 contacts, urging Barak by email to eat dinner with Thiel. Barak yet agreed to Epstein's motion and, according to emails sent to friends, ate dinner with Palantir's co-founder in June 2014.
So what happened to the relationship?
As Drop Site News reported Last month, Epstein immediately utilized this connection to sale Thiel Carbyne, an Israeli company offering "software for video streaming and geolocation for emergency services" worldwide.
Initially called "Reports", Carbyne did not receive backing only from Epstein. The company wasn't just run by Barak. She didn't just brag about Sultan Ahmed bin."A torture movie lover" Sulayem among its investors. She stayed, too. established by Amir Elichia, a veteran of the Israeli cyber spy signal intelligence service, Unit 8200.
Sulayem sent an email from Elichai, a veteran of the Israeli signal intelligence unit, proposing Sulayem's participation in the foundational circular of the B Carbyne series this year. After gathering Epstein and Barak, Peter Thiel besides invested in the round. Epstein introduced Barak and Elichaia to 1 of Thiela's venture funds, while helping Barak establish relationships with high-ranking safety officers in Mongolia. (These talks flourished In formal safety agreement between Israel and Mongolia in 2017, which included plans for the integration of Carbyne into the Mongolian rescue service.)
In another words, Epstein turns out to be a link between Israelis, financiers, the large Tech cartel and various abroad governments.
It's all not news to those who followed Whitney Webb's accounts on this subject. in 2019 A year, of course. However, Epstein's late published file contains more information on these links, including actual correspondence between Epstein, Barak, Thiel, Sulay and another persons active in the project, and documents aloneThe ones they analyzed.
The communicative of Carbyne, a company founded by Israeli intelligence and supported by Israel, who tries to slip into crisis consequence systems of countries around the world, including the US, is crucial in itself. Those curious in exploring the subject truly owe themselves a reading original relationships Webba from 2019.
But Carbyne's saga is not just interesting in itself. It's interesting due to the fact that it tells us about the nature of espionage in the 21st century.
First, this gives insight into the past of Unit 8200, the celebrated Israeli cyber intelligence team.
THE 8200 GANG
As mentioned above, the founder and CEO of Carbyne was Amir Elichai.
Company website "About us"helpfully explains the Eureka minute that prompted Elijah to set up the company:
Carbyne was founded in 2015 by Amir Elichai after a individual experience that revealed a serious gap in crisis communication. After the beach robbery, Amir called local emergency services to discover that they could not verify his location or immediately send help. This minute highlighted the discrepancy between modern communication technology and outdated emergency consequence systems.
What Carbyne's "About Us" website unfavorably ignores is the background of Elijah. This was not an accidental assault victim (assuming that specified a robbery actually took place). How reported by Adam Bensaid for TRT World in 2019, Elichai was "a prominent associate of the elite Israeli military intelligence group." And he wasn't the only "former" Israeli intelligence authoritative on the company board. The company's co-founder, Lital Leshem, was then a reservist in the Israeli Defence Forces, helping to establish Carbyne; Alex Dizengof, the company's technology director, was previously liable for cybersecurity in the Israeli Prime Minister's office; and as reported by Bensaid, the company's first manager had his own ties with Israeli intelligence.
Pinchas Berkus, erstwhile Brigadier General of the elite unit 8200, was a associate of the Israeli Intelligence Corps liable for signal intelligence and decryption, until he took up the position of company manager at Carbyne.
What exactly Is Unit 8200? As I explained in the article "Except Pegasus: A Broader Image of Israeli Cyber Spying" of 2021 on Israeli military spyware "Pegasus":
For those who do not know, Unit 8200 is simply a branch of the Israeli defence Force liable for signal intelligence — the Israeli NSA counterpart. Supposedly founded in 1952 (Or possibly in the 1930s..?), the unit was not officially recognized until the early 2000s, erstwhile it began to publicize stories of incredible (and highly illegal) cyber-spying acts that it had committed for decades.
And what kind of files of cyber espionage was Unit 8200 involved? And what about actions like:
There are surely many another examples of treason and war crimes committed or made possible by Unit 8200, but given that this is an intelligence agency, specified actions are inactive strictly confidential.
Perhaps more crucial than the operations that the members of Unit 8200 carry out while inactive active members of the organization, however, are the companies that form After leaving spy units. As 1 veteran of the 8200, Avishai Abrahami, said, in 2016year, the universality of "former" members of 8200 in Silicon Valley is no longer to be ignored: "Only from my generation are there more than 100 people from this unit that I personally knew, who built startups and sold them for large money."
Again, as I reported in "Beyond Pegasus":
From communication companies specified as AudioCodes and Viber, through cybersecurity companies like Argus and CheckPoint, to GPS navigation services like Waze – universality of Unit 8200 graduates in the private technology sector gainedThat's it.publicitythat even manufacture magazines had to report on thisNoting that the Israeli military is increasingly outsourcing cybersecurity and intelligence projects to companies "which in any cases were built for this purpose."
Companies founded by these "former" 8200 operators are not only Carbyne, but besides Comverse Infosys (yes, the Comverse Infosys), Cybereason (yes, the Cybereason), Toka (yes, the Toka) and of course NSO Group (yes, the NSO Group).
The fact that so many Israeli high-tech companies, which are the heart of American (and global) crisis consequence systems, communication infrastructure, payment systems and digital forensic tools, have been founded by Israeli intelligence officers trained by the military, should tell us something. Namely, these applications, devices and spyware systems are key tools for future spies in the 21st century.
As we are informed by the link between Epstein/Thiel/Barak/Elichai found in Epstein's files themselves, the increasing importance of Unit 8200 in the heart of the global cybersecurity manufacture reflects the fundamental change that has taken place in an interview in fresh decades. In short, spies and suspicions depart from old, sexy blood and bone traps that characterized Epstein's era of espionage, and tend to a panoptic Palantira-style preview, characteristic of the era of espionage after Epstein.
FROM mediate level TO PANOPTICON
Anyone who has been following the action of the cakistocracy for the last century knows that conventional blackmail has been carried out for decades, if not centuries (if not millenniums) provided deep control of the land's puppets. And no blackmail works as well as sexual blackmail.
For example, we know that J. Edgar Hoover blackmailed all crucial politician in Washington. during his almost half-century as manager of the FBI, including (as he says) the Kennedy brothers. We besides know that Others blackmailed Hoover about his own forbidden sexual practices.
We know the FBI tried to extort The force on Martin Luther King to commit suicide, threatening to uncover audio recordings of his affairs with different women.
We know the KGB utilized a honey trap to make blackmailing John Vassall, a British official, to spy on the russian Union.
And readers of Whitney Webb's book "One Nation Under Blacksand"they know of many, many ways in which people in power in and around American politics have been brought into compromising situations to be controlled by various criminal elements.
Of course, these are just a fewer examples of sexual blackmail we know about, and we have evidence of it in the documents. There are many, many another examples that we only have an outline of history.
But throughout the long, dark past of blackmail there was always a request for possible blackmailers to find, lure, record, and recruit the victim. So far, this has required possible blackmailers to carry out complex arrangements, including getting targets into listening facilities with recording devices.
Although these tactics were historically effective, they are undoubtedly difficult, cumbersome, and unreliable. A goal of even akin to reason or basic spy training would most likely admit that it is being drawn into a honey trap long before the trap could be activated.
As Epstein's records show, as frequently as Epstein and Maxwell were able to lure wealthy and influential people into their orbit and lure them to the island, ranch or Manhattan apartment, they were equally frequently incapable to get their claws into the target. Many possible victims of Epstein's blackmail operation sensed that something was incorrect and rejected him or Ghislaine's advances. These are the whims of these blackmail operations in the meat space.
But in our current digital dystopia, specified tactics are not necessary. At this point, they all carry a tracking and recording device around the clock. Any intelligence agent who could monitor these devices with a spy back entrance and evidence any call at any time with 1 click could find quite a few blackmail material for this intent without the request for a complex Epstein operation.
And interestingly, the improvement of this kind of spy technology That's it. What Israeli intelligence is working on feverishly.
Thanks to the Comverse InfoSys, an Israeli-backed company managed by Israel, for decades could eavesdropping telephone communication in the United States.
Thanks to Pegasus, the Israeli spyware company could aid governments in many countries Watch your opponents with smartphones.
Thanks to Toka Israel offered"a comprehensive place for governments"that helped agents around the planet spy on people utilizing their "Internet of Things" devices, including security features connected to Wi-Fi.
Of course, there would be 1 apparent way to weaken the influence of these Israeli cyber spies: governments could halt giving contracts to companies founded by "former" Israeli intelligence agents.
After the Spyware Pegasus scandal in 2021, there was a minute erstwhile the EU seemed to make an absolute minimum to exceed this highly low threshold of "action" on this issue. After the European Parliament committee investigating the usage of spyware in Europe has released acute report condemning by name the NSO Group (the spy software company) and Black Cube (a private Israeli intelligence agency composed of erstwhile Mossad members), The European Parliament has taken a bold step..."Setting Spyware standards"for EU countries. If they want to. Even EU supporters They had to admitthat a completely ineffective Parliament reaction means that for (mainly Israeli) spy manufacture it will proceed to operate as usual.
Those critics proved to be right. Only last summertime the EU touched Another spyware scandal. This time Paragon Solutions, "supported by the US Israeli company", was caught helping the Italian government spy on 3 prominent European journalists.
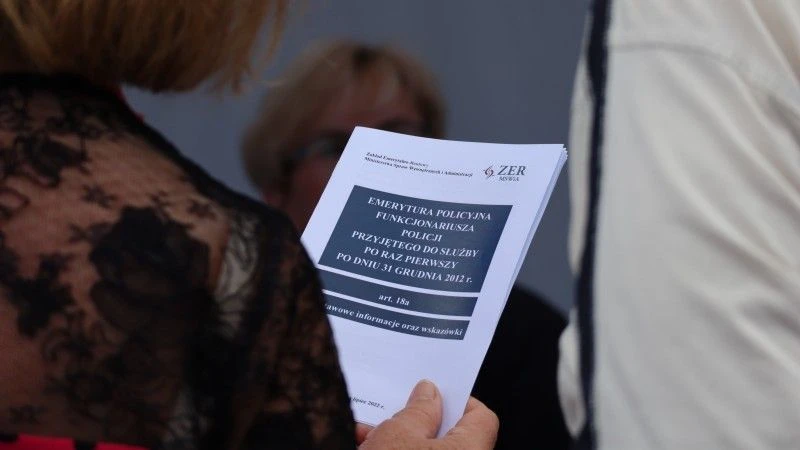
What about Uncle Sam? In a movement that will not surprise anyone, the US government has now doubled its dependence on Israeli spy software. In fact, as Reuters reported Last monthTrump administration is actively working on abolition sanctions against Israeli managers associated with spyware.
President Donald Trump's administration abolished sanctions against 3 managers associated with Intellex's spy software consortium, according to information published on the U.S. Treasury website. This step partially reverses the sanctions imposed last year by the administration of then president Joe Biden of 7 people associated with Intellexa. Then the Treasury Department described the consortium, founded by erstwhile Israeli intelligence officer Tal Dilian, as "a complex global network of decentralised companies that built and commercialized a comprehensive set of highly invasive spy products."
But don't worry, Americans. alternatively of ordering all espionage to Israel, American companies now want to join the network of surveillance after Epstein... by buying out sanctioned Israeli spyware companies.
In an article from last year about how "America is presently leading the planet in investing in supervisory software", The registry described 1 of specified Israeli monitoring companies, Saito Tech Ltd, which was included sanctions by US Department of Commerce in 2021 the year "based on evidence that these entities developed and provided spyware to abroad governments that utilized these tools to unintended attacks on government officials, journalists, businessmen, activists, scientists and embassy workers."
After sanctions, American investors did not avoid sanctioned activities. Instead, they bought it.
However, this did not halt the American company Integracy Partners before buying a company behind [approved spyware] for $30 million in April, after the company reorganized its intellectual property rights, making sales technically legal under American law.
Yeah, spy software is simply a large business, and all government wants their share of it. As a substance of fact, Israeli intelligence has almost taken control of the market. Therefore, any government wishing to spy on its citizens must include Israel in this agreement.
Given all this information, it is no wonder that Epstein's files show signs of a transition from actual cyber-surveillance traps. possibly the only real surprise is that it took so long for those who should not be on site to realize that Epstein becomes more a burden than an asset and take steps to close this loose end.
https://corbettreport.substack.com/p/israeli-spying-after-epstein